Last date modified: 2025-Oct-29
RelativityOne technical overview
Welcome to RelativityOne. Before you can set up your Relativity instance for case workflow, you will want to configure your organization's infrastructure and network access, and implement necessary security, in addition to reviewing the following system-level tools RelativityOne provides .
If you are an IT or network administrator that is charged with preparing your organization for RelativityOne, review the following system-level technical overview.
Your RelativityOne instance may contain workspaces labeled "[DO NOT ACCESS]." You are not billed for these workspaces. However, do not access or delete them. In addition, we recommend updating any views to exclude them.
RelativityOne government (FedRAMP)
The following functionality is not currently available for FedRAMP customers/government entities:
- Utility server
- Customer-managed keys (CMK)
- Sandbox environments
- Preview environment
- S2S VPN requests - Global Protect VPN client is the only supported VPN connectivity for FedRAMP customers / government entities
As a security measure, Relativity blocks all outbound connections to the internet for FedRAMP government entities by default. This may prevent the loading of linked images or interfere with the functionality of custom applications that require internet access. FedRAMP customers can request that these outbound internet connections be allowed by reaching out to Customer Support.
RelativityOne workstation configuration
Across your organization you should assess workstations to ensure that they meet Relativity minimum system requirements and have all required software installed.
- Check your browser compatibility.
- Perform workstation configuration.
Instance Settings in RelativityOne
While there are occasions in which a RelativityOne admin needs to manually adjust an instance setting that corresponds to a specific feature, instance settings in general are not applicable to RelativityOne and the Instance Settings tab itself is not visible by default.
This is due to the lower administrative burden of RelativityOne compared to Server and the fact that such administrative tasks as troubleshooting, scaling, and infrastructure management are managed by Relativity.
For this reason, we do not publish a comprehensive Instance Settings topic on this site, as we do for Server. Instead, we provide instance settings descriptions only on certain feature topics, as they pertain to that functionality.
If you need to adjust instance settings in your RelativityOne environment, please contact Support.
RelativityOne network access
For Centralized Authentication, ensure your browser allows traffic to and from the login page at login.relativity.com and *.auth0.com. See Centralized Authentication for more information.
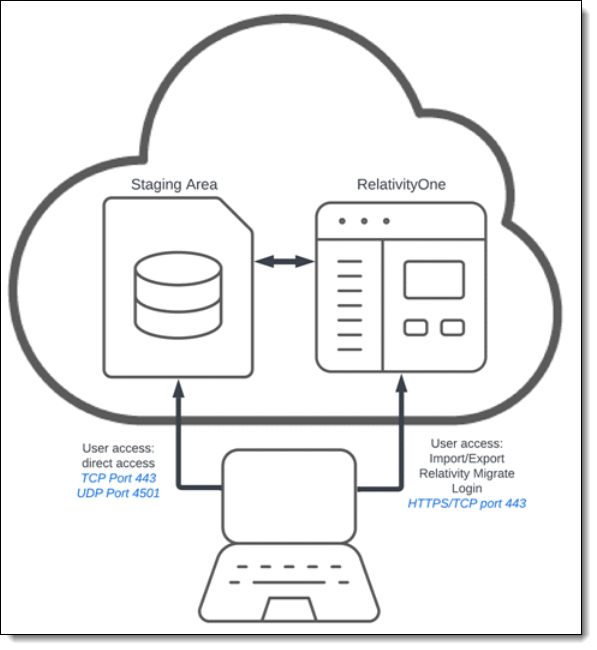
The following diagram depicts user and administrator access to the RelativityOne network in a RelativityOne instance.
Port considerations
Ensure your port settings are configured correctly for the following:
RelativityOne VPN ports
See RelativityOne VPN Ports for details.
Required ports for Data Transfer tools
For information on allowing your internal network or company configurations to use Import/Export with Express Transfer, and ROSE, see Data Transfer tools: Import/Export, Express Transfer, ROSE and Migrate - Required Ports on the Community site. You must have valid Community credentials to access this information.
Migrate
If you are using Migrate, you must allow port 443 traffic to the DNS URL corresponding to your RelativityOne instance's location.
For information about RelativityOne Government, please contact Customer Support.
| Region | Region (short) | DNS |
|---|---|---|
| Asia (East) | esas |
|
| Asia (Southeast) | seas |
|
| Australia (East) | auea |
|
| Brazil (South) | brso |
|
| Canada (Central) | cact |
|
| Europe (North) | noeu |
|
| Europe (West) | wseu |
|
| Germany (West Central) | dect |
|
| India (Central) | inct |
|
| Japan (East) | jpes |
|
| Korea (Central) | krct |
|
| South Africa (North) | zano |
|
| Switzerland (North) | chno |
|
| UAE (North) | aeno |
|
| UK (South) | ukso |
|
| US (East) | esus |
|
| US (Central) | ctus |
|
Firewall privacy considerations
You will need to allow the following:
- Fully qualified domain names (FQDN) and VPN portal URL
- Additional firewall considerations
- See R1 - Firewall Outbound IP Addresses on the Community site for outbound addresses. You must log in with your Community credentials to view this article.
Allow connections to the following:
IP address ranges and VPN portal URL
The IP addresses listed below are for both VPN and regular, non-VPN, access.
All VPN portal URL are formatted as vpn.[regional domain].relativity.one
VPN portal URL are only accessed when connecting to your Utility Server or Direct SQL via the VPN.
Primary Azure data center IP address ranges for VPN portal URL:
| Primary Azure/Entra ID region | Primary IP Range | VPN Portal URL |
|---|---|---|
| US-Central (CTUS) | 52.189.66.32/27 | vpn.ctus.relativity.one |
| US-East (ESUS) | 40.88.50.160/27 | vpn.esus.relativity.one |
| Canada-Central (CACT) | 52.228.98.0/27 | vpn.cact.relativity.one |
| UK-South (UKSO) | 51.145.60.64/27 | vpn.ukso.relativity.one |
| Asia-East (ESAS) | 52.184.89.64/27 | vpn.esas.relativity.one |
| Brazil-South (BRSO) | 191.233.244.160/27 | vpn.brso.relativity.one |
| Europe-West (WSEU) | 51.105.222.96/27 | vpn.wseu.relativity.one |
| France - Central (FRCT) | 20.199.57.128/27 | vpn.frct.relativity.one |
| Germany-West Central (DECT) | 51.116.134.160/27 | vpn.dect.relativity.one |
| Switzerland North (CHNO) | 51.107.46.128/27 | vpn.chno.relativity.one |
| Australia-East (AUEA) | 20.40.190.160/27 | vpn.auea.relativity.one |
| Korea-Central (KRCT) | 20.194.51.192/27 | vpn.krct.relativity.one |
| United Arab Emirates (AENO) | 20.203.41.32/27 | vpn.aeno.relativity.one |
| India (INCT) | 20.204.36.0/27 | vpn.inct.relativity.one |
| Ireland (NOEU) | 20.93.29.128/27 | vpn.noeu.relativity.one |
| South Africa (ZANO) | 20.87.64.160/27 | vpn.zano.relativity.one |
| Southeast Asia (SEAS) | 52.230.48.0/27 | vpn.seas.relativity.one |
| Japan (JPES) | 20.78.107.96/27 | vpn.jpes.relativity.one |
| Legacy Sandboxes | ** | vpn.ctussbx.relativity.one |
** For Sandboxes, use the FQDN listed in the next table
All VPN portal URL are formatted as vpn.[regional domain].relativity.one
VPN portal URL are only accessed when connecting to your Utility Server or Direct SQL via the VPN.
| Azure Region | VPN Portal URL |
|---|---|
| US-Central | vpn.ctus.relativity.one |
| US-East | vpn.esus.relativity.one |
| Canada-Central | vpn.cact.relativity.one |
| UK-South | vpn.ukso.relativity.one |
| Asia-East | vpn.esas.relativity.one |
| Brazil-South | vpn.brso.relativity.one |
| Europe-West | vpn.wseu.relativity.one |
| Germany-West Central | vpn.dect.relativity.one |
| Switzerland North | vpn.chno.relativity.one |
| Australia-East | vpn.auea.relativity.one |
| Sandboxes (optional) |
vpn.ctussbx.relativity.one |
Additional firewall considerations
If your firewall restricts all internet traffic, you may need to specifically allow list the WebAPI URL (i.e., https://[customername].relativity.one/relativitywebapi).Content Delivery Network considerations
Some assets on RelativityOne are now serving static content such as JavaScript, CSS, and images, via a Content Delivery Network (CDN) to enable faster content and improve availability and reliability across all geographies.
CDN overview
| Property | Details |
|---|---|
| CDN provider | Microsoft Azure |
| CDN endpoints | https://cdn.relativity.com https://cdn.relativity.us |
Network configuration
Customers must ensure that firewall or proxy configurations do not block outbound access to the Relativity CDN endpoints.
CDN services are hosted on Azure infrastructure, and IP ranges may change over time. You should use Microsoft’s published service tags or domain-based rules for accurate and maintainable access control.
Approaches to allowing access to the CDN in your environment
Option 1: Allowing the domain name
If your environment supports DNS-based rules, allow traffic to the following CDN domains:
- cdn.relativity.one
- cdn.relativity.us
This approach ensures compatibility as infrastructure evolves and avoids the need for frequent IP updates.
Option 2: Use Microsoft's service tags
Use Azure service tags to allow automatic and dynamic IP addresses.
- Relevant service tags:
- AzureFrontDoor.Frontend
- See Azure IP Ranges and Service Tags – Public Cloud on the Microsoft website to download a list of IP address ranges for Public Azure.
Option 3: Allowing IP-based address ranges (not recommended for long-term)
You can allow the current Azure CDN IP address ranges if service tag-based rules are not supported in your network setup. See Azure IP Ranges and Service Tags – Public Cloud on the Microsoft website to download a list of IP address ranges for Public Azure.
IP addresses are subject to change without notice. Hardcoding IP addresses is not recommended for long-term maintainability.
Accessing the RelativityOne backend
Typical needs for accessing the RelativityOne backend include custom reporting, application development, and data manipulation. See ee Accessing the RelativityOne backend for expanded details.
RelativityOne system downtime windows
The advantage to RelativityOne is that we maintain and upgrade your software to ensure that your business operations in RelativityOne run smoothly. It also makes sure that you always have access to the latest features and defect fixes. We require regular downtime windows to do this, typically during non-business hours.
RelativityOne resource scaling
Scaling in terms of software products refers to increasing server infrastructure resources or re-prioritizing system processes to increase a system's workload capacity on demand. Increasing a system's workload capacity either entails finishing one unit of work in a smaller amount of time, for example speed, or finishing more units of work in the same time interval, for example concurrency. Scaling is typically used for large batch operations or when there is a large volume of jobs that may take a long time.
The advantage to RelativityOne is that we maintain and upgrade your software to ensure that your business operations in RelativityOne run smoothly and that you always have access to the latest features and defect fixes.
However, we want customers to notify the RelativityOne team proactively when they know they will be bringing a large matter into the instance so that RelativityOne can be at its most powerful when handling large amounts of information ingestion and processing such as with Imaging, OCR, Branding, and Productions.
Automated RelativityOne resource scaling
RelativityOne monitors system activity and automatically makes decisions about the following:
- System resource scaling—increasing workers and server resources
- Resource prioritization—which processes should receive resources given jobs that are competing for the same resources
System resource scaling
Automatic scaling in RelativityOne detects large jobs and automatically increases system resources to a higher performance capacity. Currently, RelativityOne automatically scales resources in the following product areas:
- Processing. For example ingestion and imaging)
- Mass PDF
- OCR
- Branding
- Productions
- Indexing. For example. analytics.
Informing support of a large incoming RelativityOne project
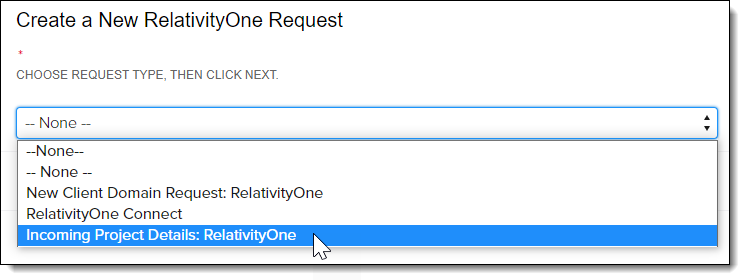
When you have a large or complex incoming RelativityOne project, it's recommended that you inform Relativity's teams so that we have enough detail to provide the guidance and resources to ensure your success. To do this, use the Incoming Project Details: RelativityOne Community form to let us know.
- Log in to the Community and click Open a Support Ticket.
- Click Submit or resume a RelativityOne request.
- Select Incoming Project Details: RelativityOne as the request type.
To complete the request, you'll be asked to provide the following information:
- RelativityOne instance or web name
- Description of the project
- The number of documents you expect to be in the workspace
- Workspace artifact ID or name
- Functionality in which you expect increased usage/volume (Analytics, Imaging, Processing, etc.)
- Start and end dates of project
Security
At Relativity, no topic is more important than security. With preventative defense, automated processes, and transparent operations, we keep your most sensitive data protected.
- Security white paper
- Client domains
- Customer lockbox
- User authentication
- RelativityOne system access privileges
Security white paper
RelativityOne runs on Microsoft Azure and is built on Microsoft’s foundational investment in security technology, operational processes, and expertise. Relativity Security utilizes logs, telemetry, and configuration data generated from the Relativity Application, underlying infrastructure, and Azure to monitor and secure the environment. No customer data or any Personal Identification Information (PII) leave the environment for this purpose.
Refer to the Security white paper for comprehensive information regarding the security built into RelativityOne.
RelativityOne Security Center
As organizations workforces are increasingly dispersed, you want to be sure you’re keeping your data secure. Security Center provides a single-threaded view into the most pressing areas of concern for securing your data.
These areas include:
- User two-factor Authentication—two-factor authentication (2FA) provides an additional layer of protection in the event that passwords are compromised. In Security Center, admins have the ability to track two-factor authentication usage and send users notifications to enable 2FA to make sure user endpoints are secure.
- Login Map—the Login Map provides you with insight into where your users are accessing data from. You will be able to see logins across geographies and identify calls to action, such as logins that do not currently have two-factor authentication set up.
- User Activity—Security Center provides insight into the status of active and inactive users and allows you to disable or delete them to ensure your data is secure.
- Lockbox access—transparency and trust are two core tenants of the security program at Relativity. Lockbox in RelativityOne ensures that Relativity support staff only have access to your workspaces when you give it to them. In Security Center, you can do real-time access audits of Lockbox/Relativity support and revoke access if needed.
- Relativity employee workspace access—this report provides transparency and real time insight into Relativity Support activity in your Relativity instance to help you work with our Support teams. It offers a list of easy-to-read audits of Relativity staff activity that you can export to CSV format for external review.
- Threat Intel—the Threat Landscape Update (TLU) report is a review of the threat actors, malware, techniques, campaigns, and other threat information currently active that has an impact on the legal services industry. The report publishes weekly.
Only RelativityOne System Administrators have access to the Security Center dashboard.
See RelativityOne Security Center.
Hash value instance settings for billing metrics
The following instance settings determine whether the billing telemetry data we collect from your RelativityOne instance is anonymized or not.
Examples of billing telemetry data would be Workspace sizes, client and matter values, or usernames. We collect this data to accurately report your RelativityOne billing metrics. Configure these instance settings according to your organizations' security standards to choose whether we collect them in an anonymized way.
Modifying these settings has a downstream impact on your Billing API. When anonymization is enabled, the API returns hashed data. For more information see,
These settings will affect what data is displayed on your
In Cost Explorer, data is unhashed, except for historically removed objects, which remain anonymized.
| Instance Setting | Section | Description |
|---|---|---|
| ReplaceCaseNameWithArtifactID | kCura.Billing | Controls whether the Case Name in the billing metrics is replaced with the Case ArtifactID. If set to True, the Case Name in the billing metrics is replaced with the Application ArtifactID. By default, the value is set to False, and the Case Name is displayed. |
| ReplaceClientNameWithHashValue | kCura.Billing | Controls whether the Client Name in the billing metrics is replaced with a unique hash value. If set to True, the Client Name in the billing metrics is replaced with a unique hash value. By default, the value is set to False, and the Client Name is displayed. |
| ReplaceClientNumberWithHashValue | kCura.Billing | Controls whether the Client Number in the billing metrics is replaced with a unique hash value. If set to True, the Client Number in the billing metrics is replaced with a unique hash value. By default, the value is set to False, and the Client Number is displayed. |
| ReplaceMatterNameWithHashValue | kCura.Billing | Controls whether the Matter Name in the billing metrics is replaced with a unique hash value. If set to True, the Matter Name in the billing metrics is replaced with a unique hash value. By default, the value is set to False, and the Matter Name is displayed. |
| ReplaceMatterNumberWithHashValue | kCura.Billing | Controls whether the Matter Number in the billing report is replaced with a unique hash value. If set to True, the Matter Number in the billing metrics is replaced with a unique hash value. By default, the value is set to False, and the Matter Number is displayed. |
| ReplaceUserNameWithHashValue | kCura.Billing | Controls whether Relativity replaces the username portions of user email addresses with hash values in billing information sent manually or sent automatically through the SMTP server. If set to True, Relativity replaces all text preceding the @ symbol in each user email address with a unique hash value. Domains remain unencrypted. If set to False, the entire user email address appears. |
Client domains
The client domains feature enables Relativity to deliver more powerful managed service offerings for service providers in a single Relativity
Using client domains, system admins can empower a user group that is not part of the System Administrator group, client domain admins, to perform common administrative tasks within their own client domain while limiting their visibility into the Relativity environment as a whole. The client domain admins can customize the permission settings to various objects according to their preferences within their own domain, but cannot access any permissions outside of that. This resource isolation functionality grants your enterprise clients more administrative control over their own portions of the environment while preventing back-end visibility and unauthorized changes to your Relativity
Client domains are targeted for the above use case only and it is important to consider all the limitations outlined in
Implementing client domains requires an additional license from Relativity ODA LLC. Each client domain license is unique, and client domains can have different terms encoded on their license keys. The license for a client domain is unrelated to any other license for Relativity (e.g., number of seats). Client domain licenses are not transferable from one client to another.
See Client domains.
Customer lockbox
RelativityOne’s Lockbox feature provides you with greater control over your workspace data and access. It helps protect sensitive information from unauthorized access by Relativity System Admins, while still allowing authorized users to access data for legitimate purposes. Lockbox is designed to protect your workspace data by preventing access by Relativity support and operations teams, even if they have administrative privileges. By default, this feature is enabled, which means that any system administrator, including those on the Relativity team, cannot see your workspace data without explicit permission.
Consider the following:
- RelativityOne Lockbox has granular control that is managed through separate EnableRelativityLockbox and EnableCustomerLockbox instance settings. This allows for a precise configuration based on your specific needs.
| Instance setting name |
Description |
Value | Impact |
|---|---|---|---|
|
EnableRelativityLockbox |
Controls access to workspaces for all Relativity employees, except those explicitly granted access by the customer. |
True |
Prevents all Relativity employees from accessing workspaces unless they are added to workspace groups. This requires manual intervention by the customer to grant access to Relativity employees. |
| EnableCustomerLockbox |
Controls access to workspaces for Client System Administrators. |
True |
Prevents Client System Administrators from accessing workspaces unless they are added to workspace groups. This requires Client System Administrators to disable Lockbox to access workspaces, which triggers alerts to be generated. |
- You can view and manage security permissions for Relativity Support team users on the security permissions page unless you choose to lock them out entirely.
- If you want to monitor workspace actions taken by Relativity employees, you can use the Security Center's Relativity employee workspace access feature. Additionally, you can use the Lockbox access feature of the Security Center to remove Relativity employee access from your workspaces if desired.
- When the EnableCustomerLockbox instance setting is enabled or disabled, a Security Alert is automatically generated. This helps you keep track of any changes to your workspace's security settings.
- To enable Lockbox for Relativity employees and prevent them from adding themselves to workspace groups, set the EnableRelativityLockbox instance setting to "True".
- To allow your System Administrator to access workspaces, set the EnableCustomerLockbox instance setting to "False".
- To grant Relativity support temporary access to a workspace, you can either add Relativity support to a group that belongs to the workspace, or set the EnableRelativityLockbox instance setting to "False".
When you contact Relativity Support for troubleshooting, the following high-level steps are performed if access to customer workspace is required to resolve an issue:
- Support is requested through the usual means.
- The Relativity Customer Support technician will request that you add a RelativityOne Support group to the workspace in question.
- The Relativity Customer Support technician will troubleshoot your case per standard protocol.
- Upon resolution, the Relativity Customer Support technician will advise you that the issue is resolved.
- You should then remove the RelativityOne Support group from the workspace you added them to.
See Customer lockbox.
Customer-managed keys (CMK)
This functionality is not currently available for FedRAMP customers / government entities.
CMK is not currently offered as part of the Relativity PayGo model.
Customer Managed Keys (CMK) give you control over the keys that encrypt data at rest in RelativityOne by enabling you to own and control your own keys through third-party key management solutions for persistent data in RelativityOne.
The scope of the feature covers RelativityOne services that retain persistent data, which includes:
- File
- SQL
- Audit
- Analytics
- Secret Store
If you have any issues, please contact Relativity Support with “R1 – CMK – ” in the subject.
See Customer-managed keys (CMK) for more details.
User authentication
Relativity
Relativity
- Password—a method that includes a user name, the user's email address, and a password.
- OpenID Connect—a protocol for an external identity provider, authenticating against an external identity provider using the OpenID Connect protocol. OpenID Connect is a modern authentication protocol can be used to connect to providers such as Azure Active Directory. See OpenID Connect for more information.
- SAML 2.0—a method that authenticates against an external identity provider using the SAML 2.0 protocol. SAML 2.0 is an older authentication protocol that is still in widespread use. See SAML 2.0 for more information.
- When implementing single sign-on (SSO) across Relativity instances, the following scenarios are supported:
- Identity Provider-initiated SSO using SAML 2.0
- ID provider and service provider-initiated SSO with OpenID Connect
- To log in using PIV/smartcard, configure RelativityOne with an OpenID Connect or SAML provider that supports PIV/smartcard logins. PIV/smartcards are not directly supported in RelativityOne.
In addition to the above protocols, Relativity has the following additional authentication features:
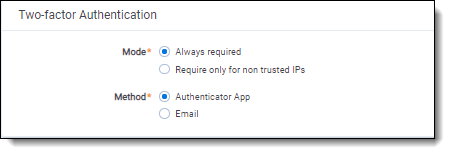
- Two-factor Authentication—when logging in with the Password method, you can require the user to pass an additional two-factor check based on an email or message sent to the user's phone, through a mobile email gateway.
- Mode—always required or require only for non-trusted IPs
- Method—Authenticator App or email. For more information, see the authenticator app's documentation.
- Trusted IP Range—limit access to the Relativity application based on the user's source IP address.
See Authentication.
RelativityOne system access privileges
Relativity initially issues the credentials for the items below. However, after credentials are sent, you will directly manage the following access credentials:
- VPN—password is active for 90 days. When it expires and you must reset it as the customer. You will need your original password in order to complete the password reset or you will need to contact Support for a new temporary password.
- Direct SQL—does not expire
- Utility Server—does not expire
When someone leaves your organization who has been issued one of these access credentials, you should open a Support ticket to have that person's user access removed. We recommend that you track who in your organization has access to these credentials, and make submitting a Support ticket part of the employee exit process.
Setting up a hybrid environment
Relativity server and RelativityOne
With the introduction of RelativityOne, hybrid environments (combining cloud and on-premises instances) are becoming a common deployment scenario. The Relativity hybrid model provides a compelling alternative to on-premises hosting of cases.
Hybrid environment business scenarios:
- Your organization decided to start migrating older cases to RelativityOne
- Your firm’s IT department then no longer has to provision more hardware for new cases
- Simply migrate old cases to RelativityOne to free up infrastructure in your local data center
Relativity hybrid model allows you to start new cases in the RelativityOne instance with benefits such as:
- Avoiding the hassle of provisioning hardware to support those cases
- Viewing/accessing cases in a different instance
- Single sign on across instances (when using OpenID Connect protocol)
Despite the benefits of this hybrid model, RelativityOne is a separate instance with a separate user store and separate credentials. You must manage user credentials across two different systems - a task that can be time consuming and prone to errors.
Refer to the following topics for more information:
Personalization
Consider the following regarding personalization in RelativityOne:
- Custom logo—customers can request a custom logo that will display on the login screen and optionally in the upper right corner of the instance next to the "Hi, User!" drop down from their Relativity implementation specialist or customer success manager. The logo submitted should be a maximum height of 50 pixels; width may vary dependent on the style of the logo
- Custom URL—Relativity does not provide unique URLs for customers. Your RelativityOne URL will always be formatted as: https://<organization name>.relativity.one.
If you have questions on personalization, contact Support.
Regional date settings
Relativity now supports the modification of the default regional date format setting for customer Relativity instances. For example, setting the regional date format to DD/MM/YYYY for an instance in Australia vs. the current default US date format MM/DD/YYYY. When completing your RelativityOne onboarding questionnaire, discuss considerations for changing regional date setting in your instance with your Relativity Implementation Specialist. If you are already a customer and want to make this change, please contact your CSM.
Once this change is made by Relativity for your instance, the following will be true:
- Email regional date considerations:
- Emails processed prior to a regional date format change will have a different date format in the header text than those processed after the change. For email chains with different date formats in the email (e.g., emails sent from other regions) the extracted text does not change and it’s retained simply as extracted text.
- Email threading dates will still be impacted if the Use Email header fields setting is set to No.
- Imaging / Save as PDF regional date considerations:
- Images created before a regional date format change will have a different date format than images after the change.
- DATE fields used for branding images (with designations) will always be in US date format.
- When imaging a document, if you select “replace field codes” (which replaces auto-filled dates), and you choose a DATE field in Relativity, it will always replace the date in US format.
- When branding during a Save As PDF action, if you select a DATE field, it will always be in US date format.
Consideration should be given when importing workspaces from instances with different regional date setting as there may be inconsistent date formats with Processing or when using Save as PDF/Imaging features. Additionally, pre-Foxglove RelativityOne release, deduplication output will be inconsistent if different regional date formats were used. The hashing algorithm changed in the Foxglove RelativityOne release to ensure deduplication is not impacted when a workspace with non-US date format is restored, however manual corrective steps, including executing a script, will be required before additional data can be processed into the workspace. Please reach out to Support for information on these manual steps.
Custom application development in RelativityOne
RelativityOne platform API
The RelativityOne platform provides a rich set of APIs that enable you to enhance the functionality of the Relativity system by creating customized applications that meet the specific e-discovery needs of your business.
Refer to RelativityOne developer considerations for more information.
Sandbox
RelativityOne Sandbox refers to reusable RelativityOne environments that allow you to test SQL scripts, event handlers, API based applications, custom pages, and custom agents.
Sandbox is a service that you must subscribe to. Please contact your Account Manager for more details. Sandboxes are free with 10TB and up subscriptions. Subscriptions less than 10 TB can opt to purchase Sandboxes.
See RelativityOne Sandbox for more information.
Preview
Preview refers to a free RelativityOne instance that gives you early access one month ahead of your RelativityOne upgrade. This enables you to identify feature changes that impact your workflows and adjust accordingly. The Relativity Preview feature, lets you try out the new version of Relativity prior to release in an environment that has the same Security and feature functionality of a RelativityOne instance.
Relativity Preview offers you the the following benefits:
- The ability to preview workflow changes in the UI prior to a production release.
- Seamless integration with RelativityOne production instance via User Sync and Federated Instances.
- Preview is pre-loaded with dummy data that effectively demonstrates new Relativity features.
This functionality is not currently available for FedRAMP customers / government entities.
System logging in RelativityOne
RelativityOne does not provide external access to logs except in Sandbox test environments; if a log is needed, we encourage you to contact Support in order to troubleshoot these sorts of issues.
RelativityOne SMTP services (e-mail)
Customers have access to an SMTP server that will send password reset / invitation emails, and other system notifications such as job notifications. These settings are not configurable in RelativityOne and the email will come from a generic relativity.one address.
On this page
- RelativityOne technical overview
- RelativityOne government (FedRAMP)
- RelativityOne workstation configuration
- Instance Settings in RelativityOne
- RelativityOne network access
- Accessing the RelativityOne backend
- RelativityOne system downtime windows
- RelativityOne resource scaling
- Security
- Hash value instance settings for billing metrics
- Setting up a hybrid environment
- Personalization
- Regional date settings
- Custom application development in RelativityOne
- Sandbox
- System logging in RelativityOne
- RelativityOne SMTP services (e-mail)